Configure → Drift → Breach → Repeat: The Cycle of Cybersecurity Control Configuration Risk
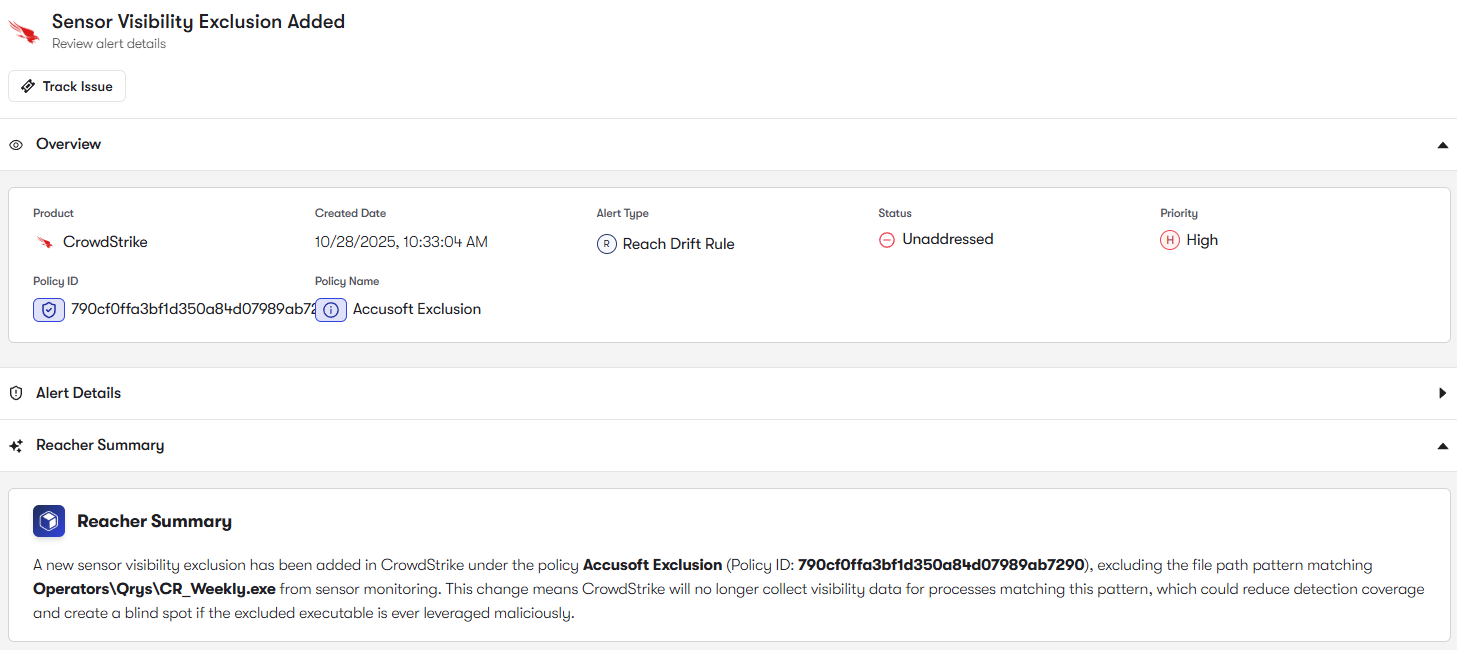
Get the reportBut as environments scale, Falcon configurations can drift. Prevention policies may operate in monitoring mode, sensors may be outdated, and endpoint hardening features may remain underutilized.
Falcon protection depends on consistent sensor deployment and version coverage across endpoints. Reach analyzes Falcon host inventory and sensor telemetry to find and fix unmanaged devices, endpoints missing the Falcon sensor, or hosts running outdated sensor versions.
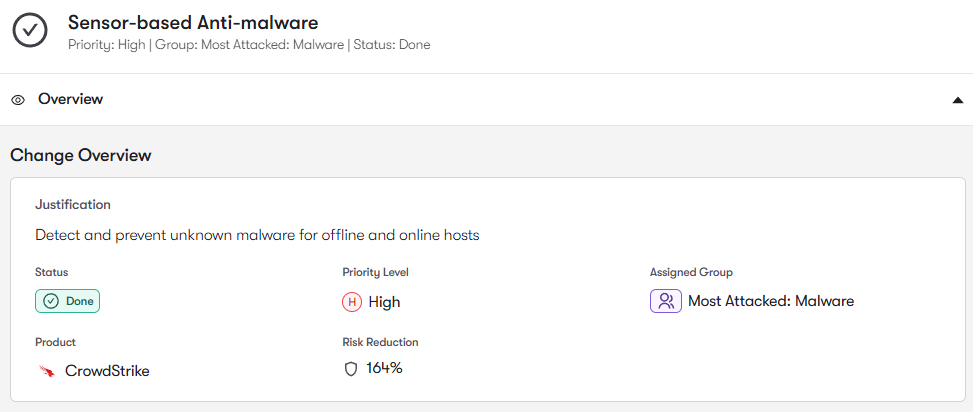
CrowdStrike Falcon uses prevention policies to block malware, suspicious behaviors, and exploit attempts on endpoints. Reach analyzes settings across host groups to identify and remediate devices operating in detection-only modes, weakened malware protection settings, or inconsistent policy enforcement.
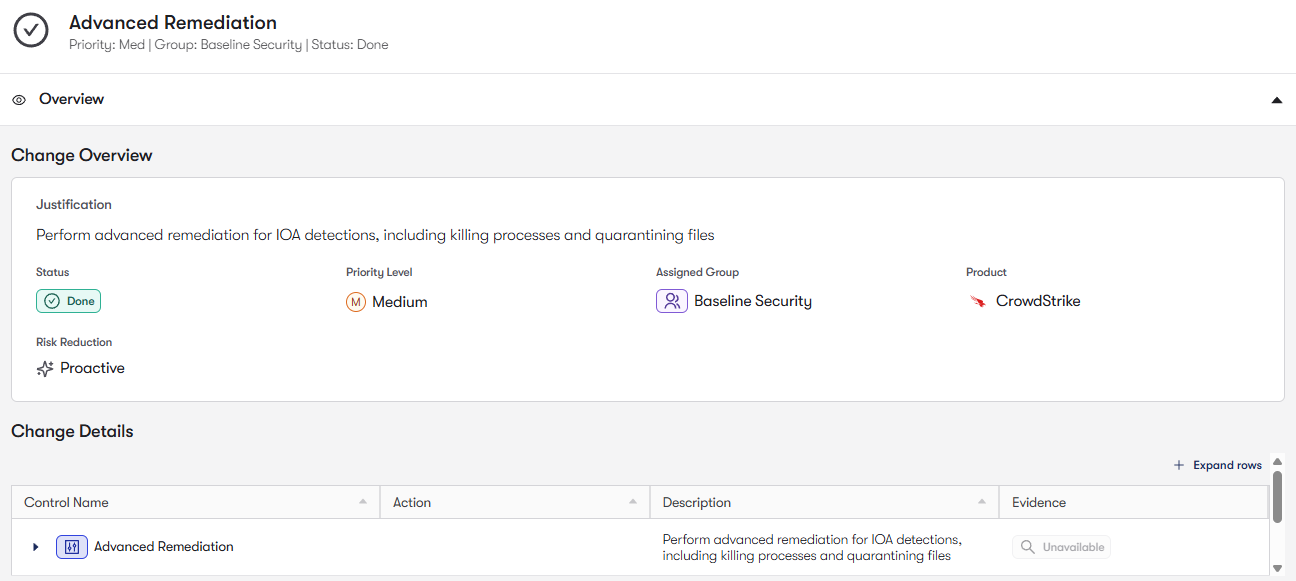
Falcon relies heavily on Indicators of Attack (IOAs) and behavioral analytics to detect attacker techniques such as credential theft, lateral movement, and script-based attacks. Reach analyzes detection configurations and policy settings to identify and remediate disabled behavioral protections or detection gaps across endpoint groups. This helps Falcon detect advanced attacks that traditional signature-based tools would miss.
Falcon policies are typically applied through Host Groups, where different device types receive different protection policies. Reach analyzes policy alignment across Host Groups to detect configuration drift and inconsistent prevention policies. By maintaining consistent security controls across all endpoints, Reach ensures Falcon delivers uniform protection throughout the environment.

To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: