Configure → Drift → Breach → Repeat: The Cycle of Cybersecurity Control Configuration Risk
Get the reportBut Conditional Access policies, authentication requirements, and risk-based protections can drift over time, creating gaps in protection.
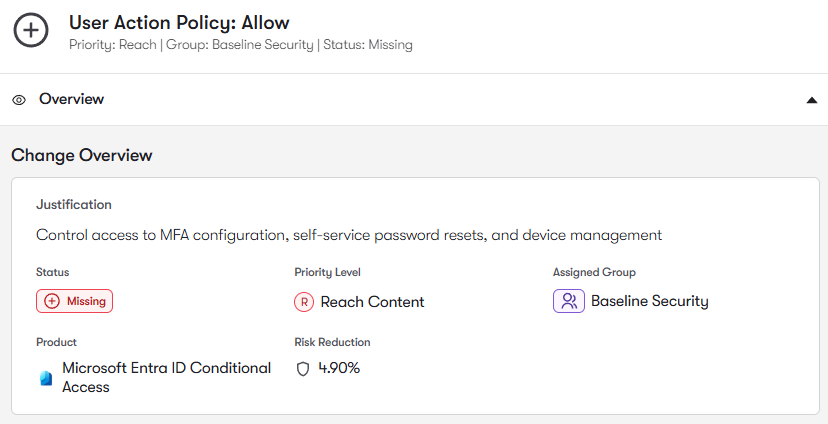
Conditional Access policies determine when and how users must authenticate before accessing applications. Reach analyzes policy coverage across users, groups, and applications to identify authentication paths not protected by Conditional Access, and then recommends policies to be consistently applied for optimal protection.
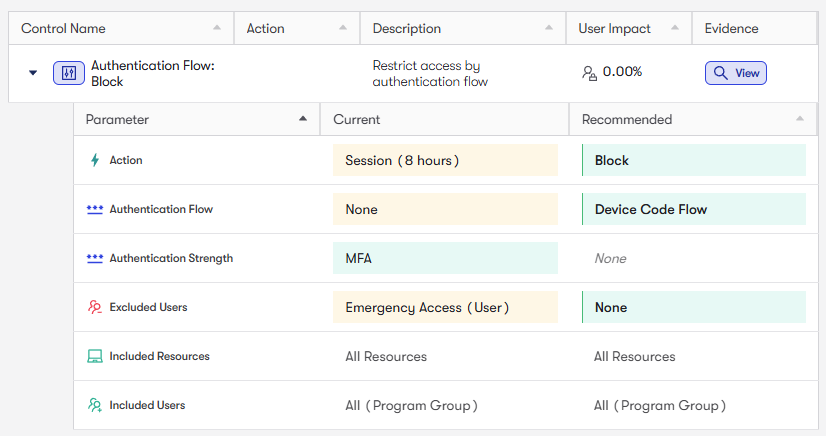
Reach analyzes Conditional Access authentication requirements and identifies users, applications, or sign-in scenarios where MFA is not enforced or inconsistently applied. Reach can remediate these misconfigurations with just a few clicks for rapid risk reduction.
Conditional Access policies often contain exclusions, exceptions, or named location allowances designed to maintain usability. Over time, these exclusions can create unintended authentication bypass paths. Reach rapidly finds and fixes these misconfigurations and detects when these policies drift from security baselines.
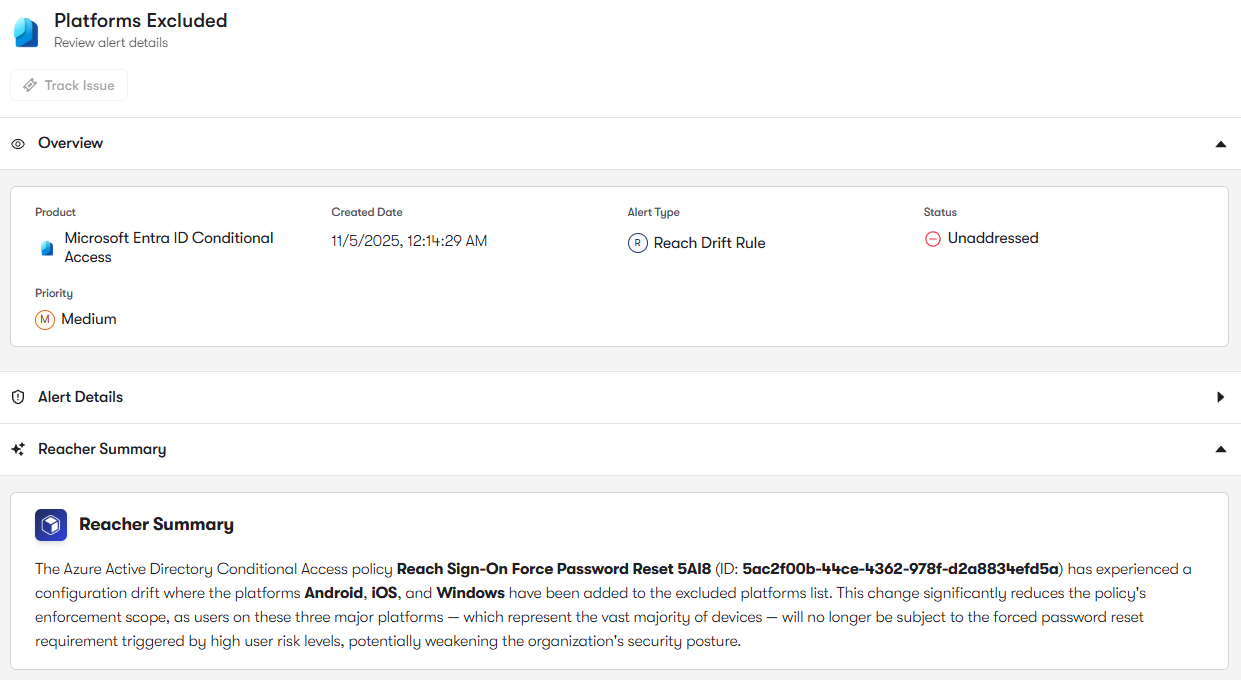
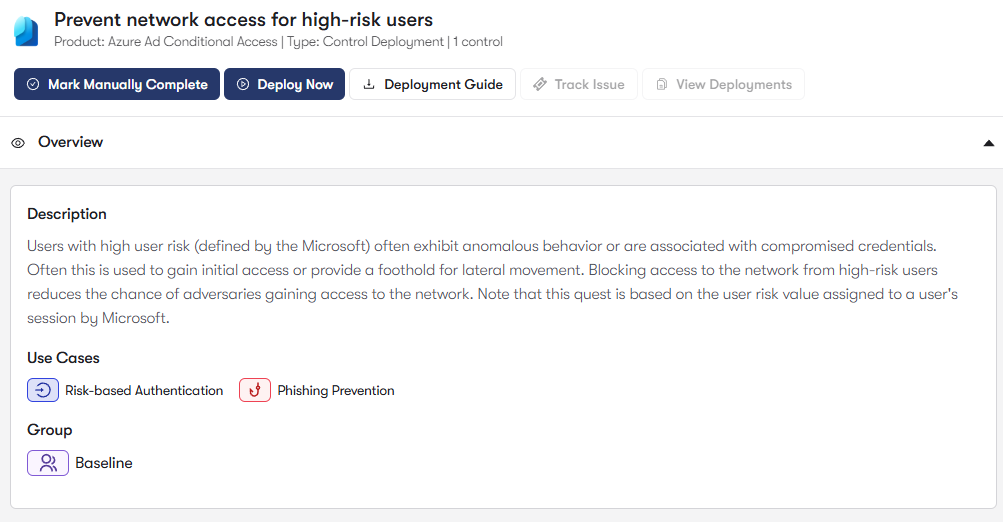
Entra ID provides sign-in risk and user risk policies that respond to suspicious authentication activity. Reach analyzes these risk-based policies to identify environments where automated risk responses are not fully configured or enforced. It highlights opportunities to require stronger authentication or block high-risk sign-ins.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: