Configure → Drift → Breach → Repeat: The Cycle of Cybersecurity Control Configuration Risk
Get the reportBut as environments scale and changes are made, Defender for Endpoint security controls can drift away from security baselines, leaving your organization more susceptible to risk.
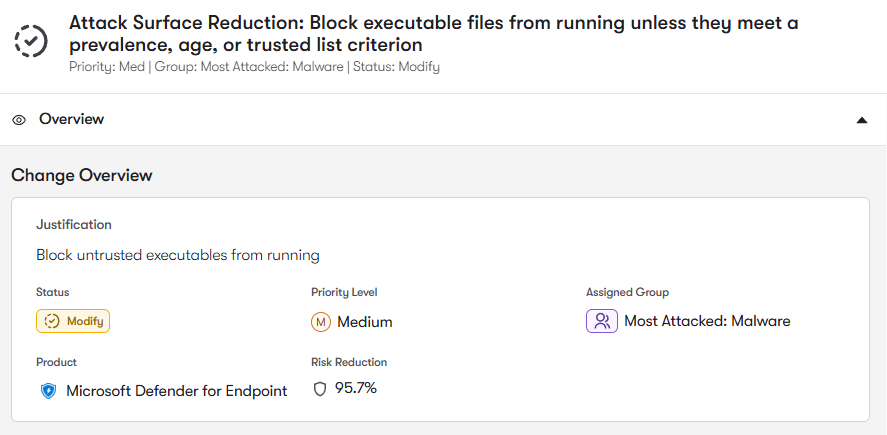
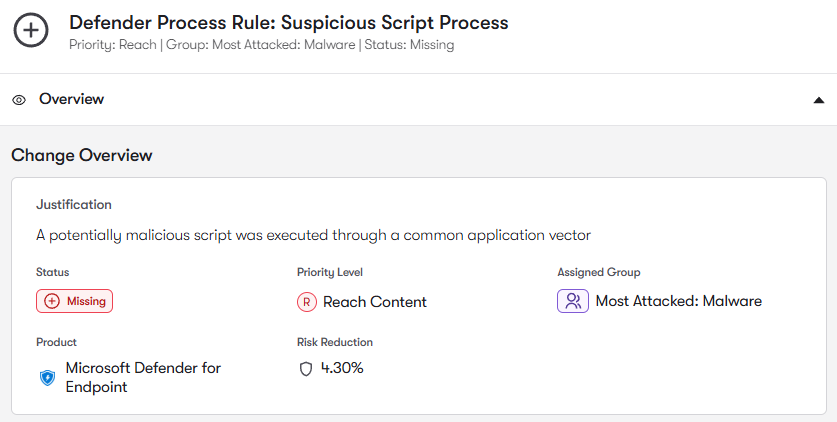
Reach analyzes ASR rule configurations to identify rules that are disabled, operating in audit mode, or inconsistently enforced across device groups. It also highlights gaps where critical ASR protections are missing. By strengthening ASR enforcement, Reach helps prevent attackers from using common post-exploitation techniques.
Reach analyzes device inventory and onboarding status to identify endpoints that are not protected by Defender or are running outdated configurations. By ensuring complete onboarding coverage, Reach helps security teams maintain full visibility and protection across all endpoints.
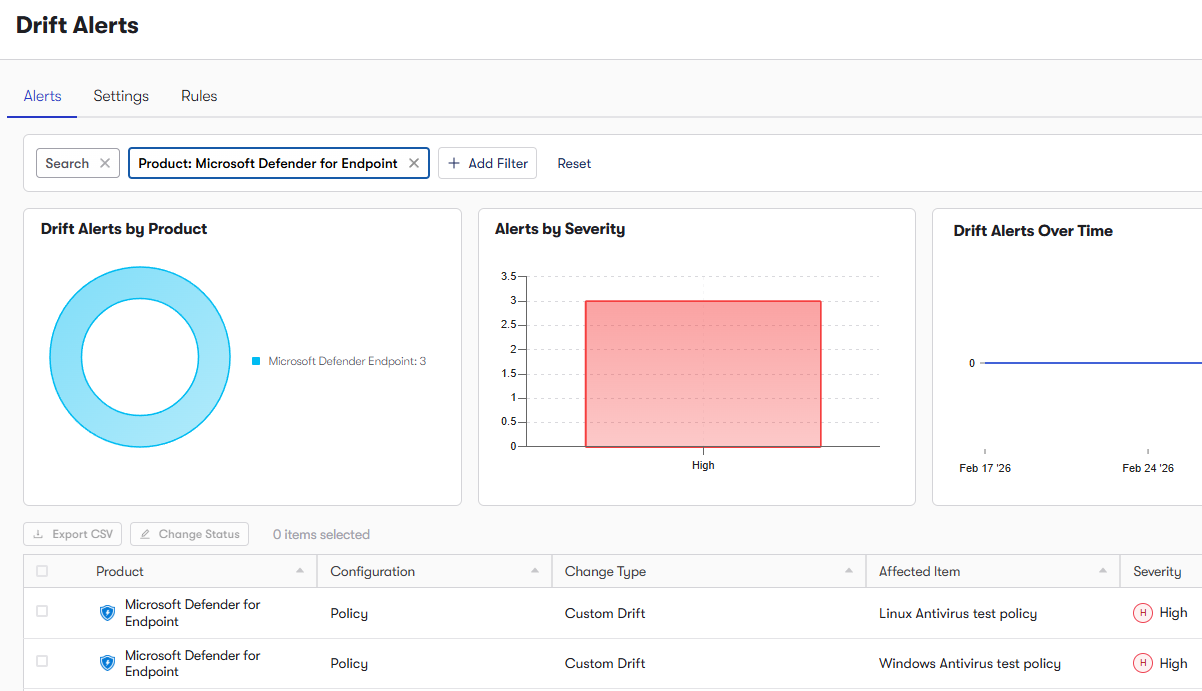
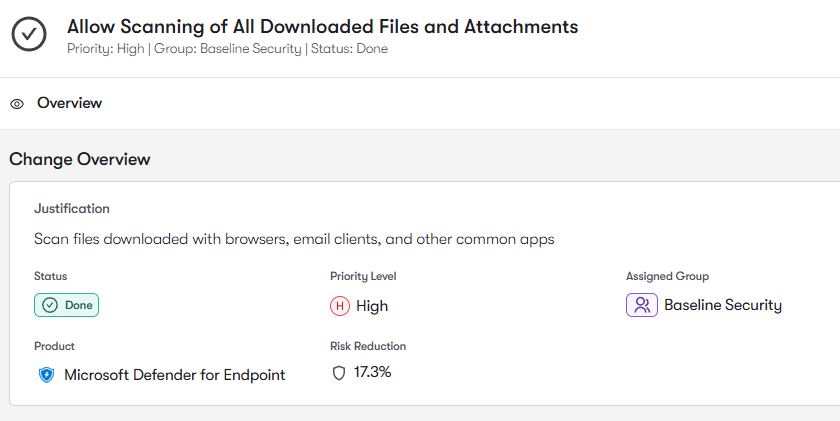
Reach analyzes endpoint security policies and Microsoft Security Baselines to identify and remediate inconsistent configurations, weakened malware protection settings, or misaligned enforcement across device groups. This ensures that devices maintain strong, consistent protection against malware and exploit attempts.
Defender for Endpoint includes powerful Exploit Protection and attack surface reduction controls designed to block exploitation techniques and reduce the number of attack paths available on endpoints. Reach analyzes exploit mitigation settings and device hardening configurations to identify, and ultimately correct, underutilized protections or incomplete policy coverage.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: