Configure → Drift → Breach → Repeat: The Cycle of Cybersecurity Control Configuration Risk
Get the reportBut endpoint security controls, prevention, detection, and response capabilities can drift away from security baselines and best practices, creating gaps in protection.
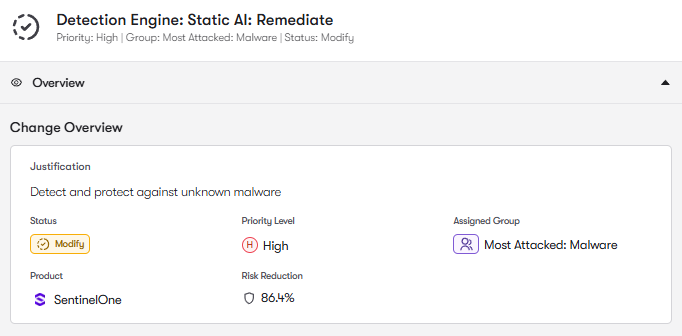
Reach pinpoints the SentinelOne EDR, EPP, and XDR settings that most directly affect protection and helps teams move them into stronger states. From malware prevention to script and fileless attack response, Reach highlights what needs attention and guides the fix.
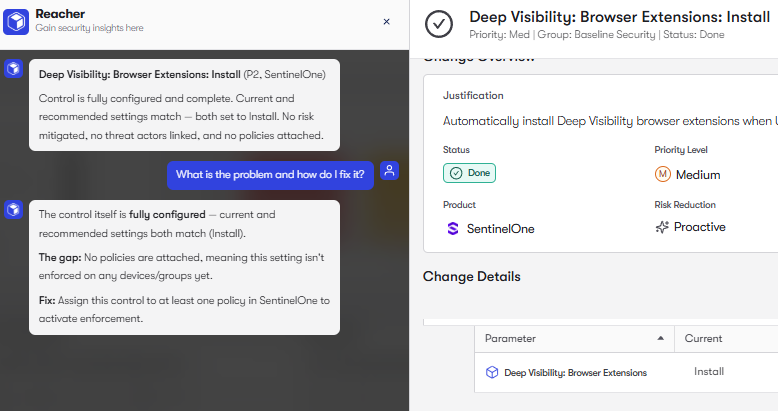
Reach surfaces underused SentinelOne Singularity Endpoint Security capabilities that limit visibility, investigation, and response. By helping teams enable the right telemetry and hardening controls, Reach increases investigative depth and makes the platform more effective in daily operations and active incidents.
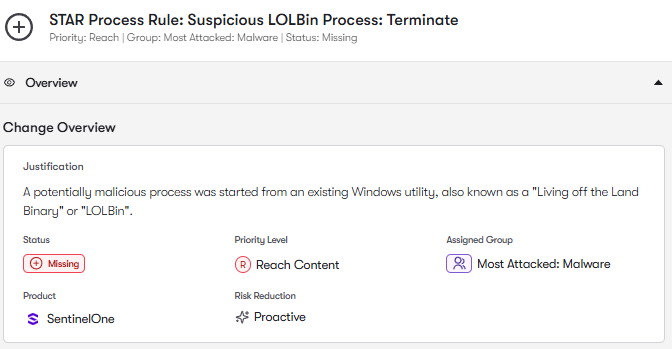
Reach identifies missing detection content that leaves common attacker behavior unchecked. By surfacing gaps across phishing, malware, suspicious scripts, LOLBin abuse, and external communication, Reach helps teams expand coverage where it matters most.
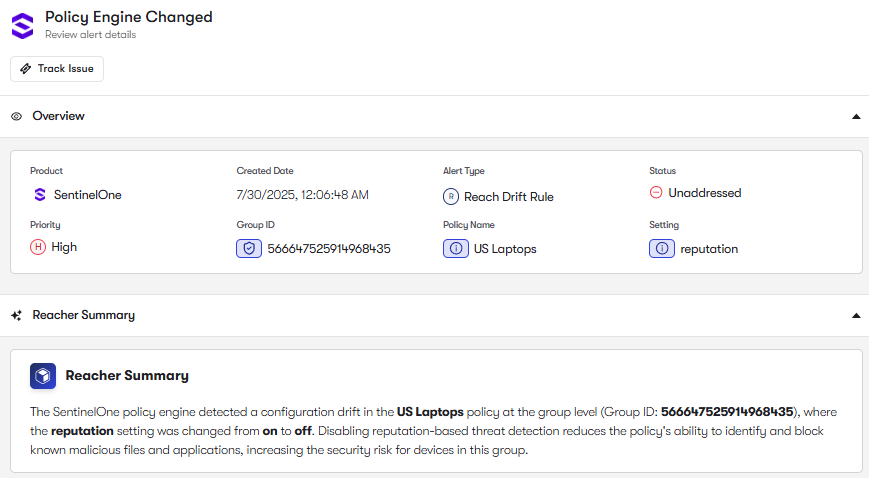
Reach continuously monitors SentinelOne for drift and alerts teams when approved settings change. Whether a policy is weakened or an exclusion is added or modified, Reach shows what changed and how to bring it back in line.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: