Configure → Drift → Breach → Repeat: The Cycle of Cybersecurity Control Configuration Risk
Get the reportBut collaboration settings often introduce hidden security risks. External Access policies, Guest Access permissions, and Meeting Policies can drift over time, creating opportunities for social engineering, unauthorized access, or identity abuse within trusted communication channels.
Teams allows organizations to communicate with external domains through External Access (Federation) policies. Reach analyzes these configurations to identify overly permissive federation settings that allow unrestricted communication with external organizations. It also highlights environments where domain restrictions are not properly configured. By tightening External Access policies, Reach helps reduce the risk of external social engineering and phishing attempts targeting users within trusted Teams conversations.
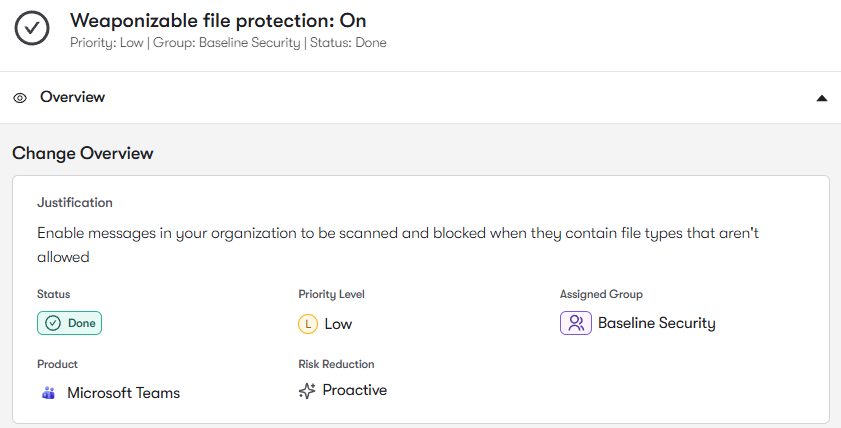
Teams enables collaboration with partners and vendors through Guest Access policies that allow external users to join Teams and access shared content. Reach analyzes guest access configurations to identify overly permissive settings, unmanaged guest accounts, or policies that allow excessive data sharing. These gaps can expose sensitive information or create opportunities for unauthorized access. By strengthening Guest Access governance, Reach helps organizations maintain secure collaboration with external partners.
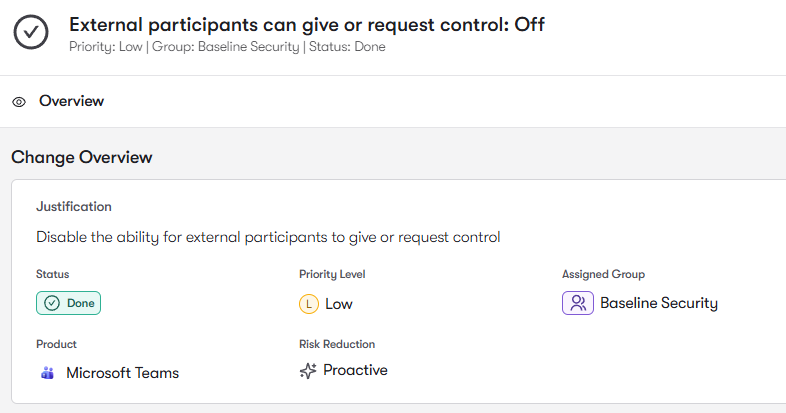
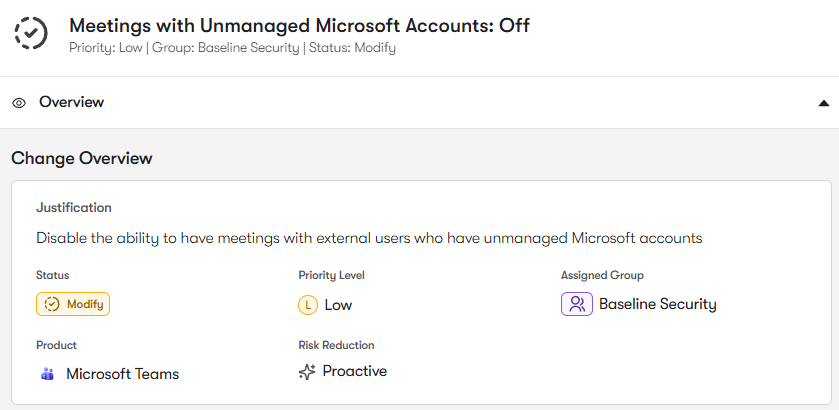
Teams meetings are governed by Meeting Policies, which control features such as lobby bypass, anonymous meeting participation, and screen sharing permissions. Reach analyzes these settings to identify policies that allow anonymous users to join meetings or bypass lobby controls without proper verification. These configurations can enable impersonation or unauthorized meeting participation. By securing Meeting Policies, Reach helps prevent identity abuse and unauthorized access during meetings.
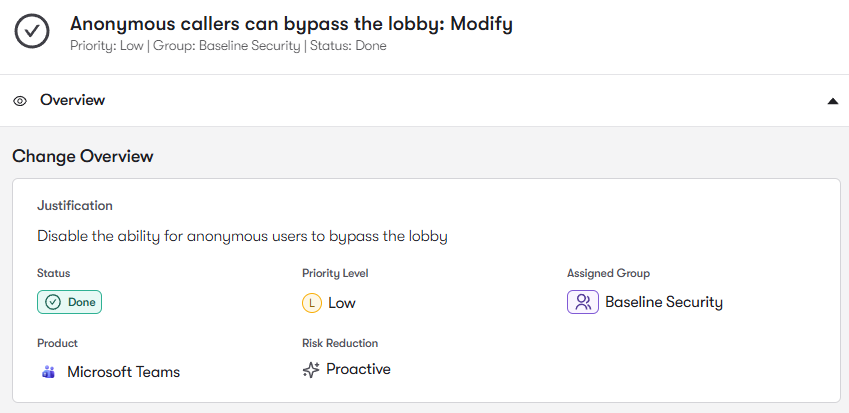
Teams environments constantly evolve as administrators adjust collaboration settings and introduce new policies. Reach continuously monitors configuration changes across External Access policies, Guest Access controls, Meeting Policies, and Teams Admin settings to detect configuration drift. When collaboration controls weaken over time, Reach alerts security teams and recommends corrective actions. This ensures Teams security settings remain aligned with organizational security intent.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: