Just Released: Reach Recognized in Gartner® Emerging Tech Report on Domain-Specific Language Models for SecOps
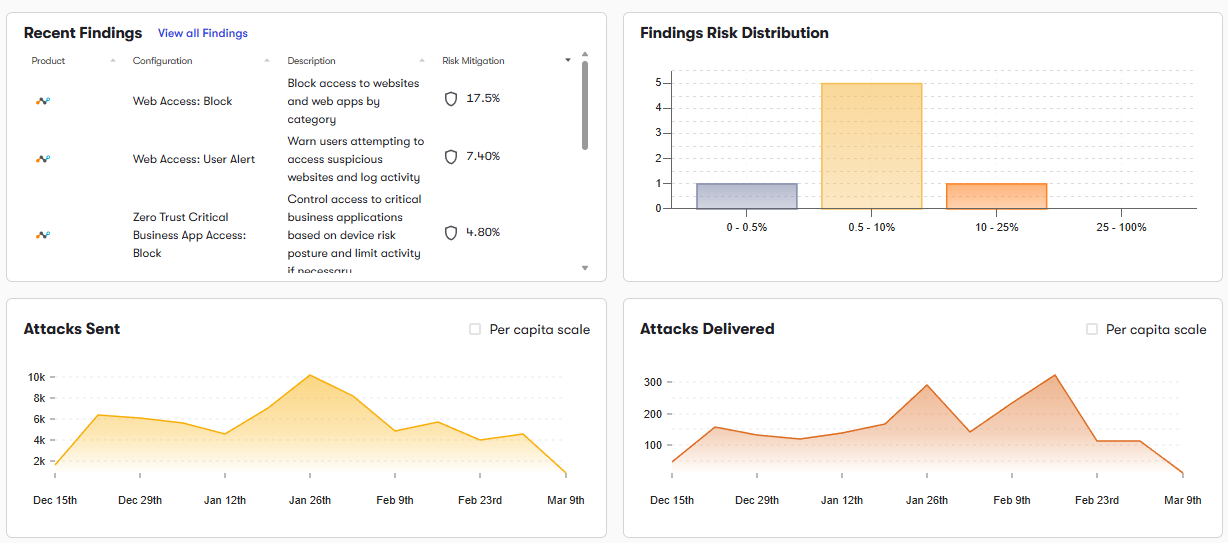
Get the reportBut ASR rules, security policies, and onboarding can drift, leaving endpoints with weaker protections.
Reach analyzes ASR rules to identify disabled, audit-mode, or inconsistently applied protections. Strengthening these blocks common attacker techniques.
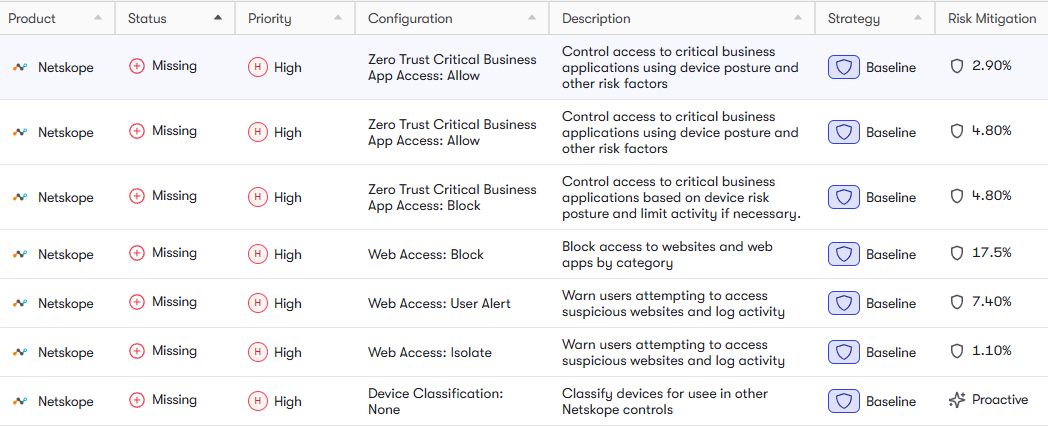
Reach identifies endpoints not onboarded or running outdated configurations. This ensures full visibility and protection across devices.
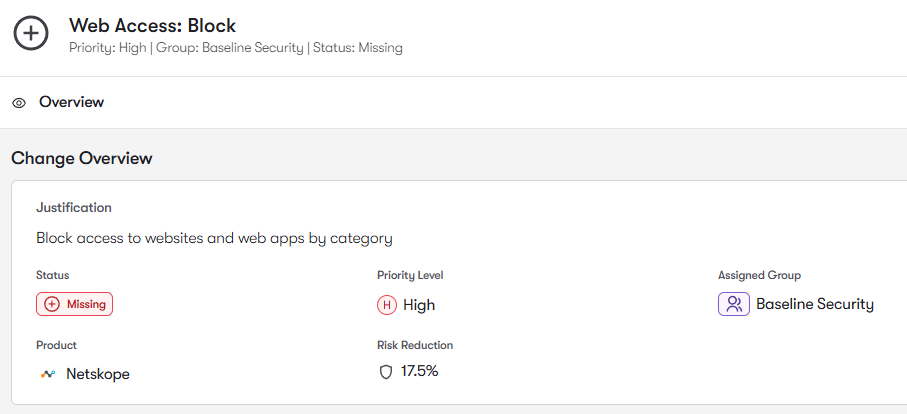
Reach analyzes security policies and baselines to identify inconsistencies or weak configurations. Optimizing these ensures consistent protection.
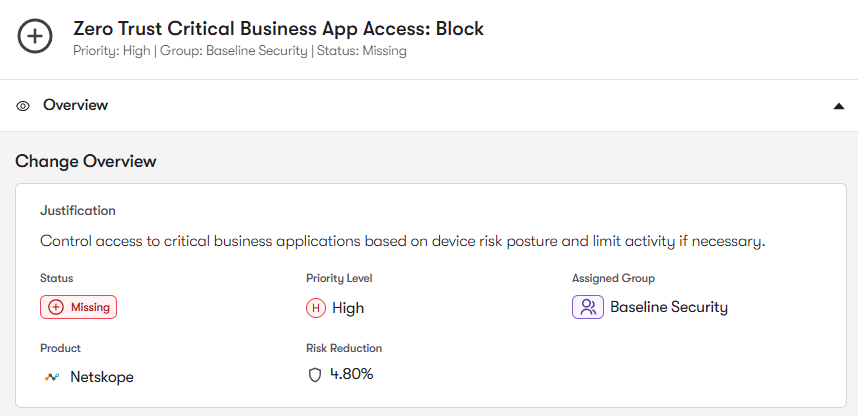
Reach identifies gaps in exploit protection and hardening controls. Enforcing these reduces attack surface and prevents exploitation.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: