Just Released: Reach Recognized in Gartner® Emerging Tech Report on Domain-Specific Language Models for SecOps
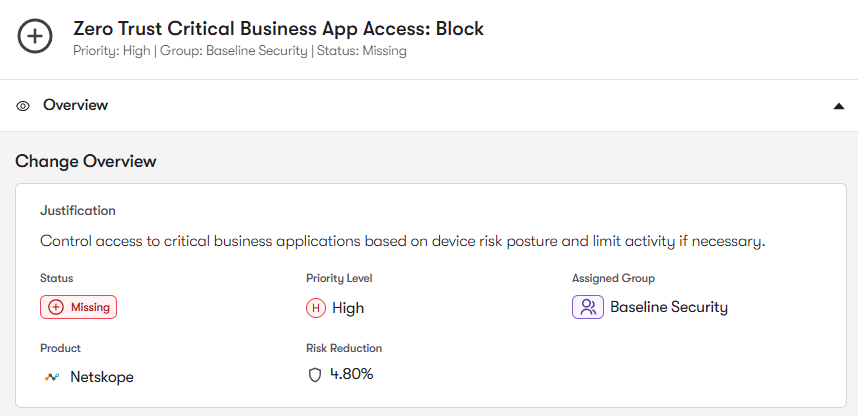
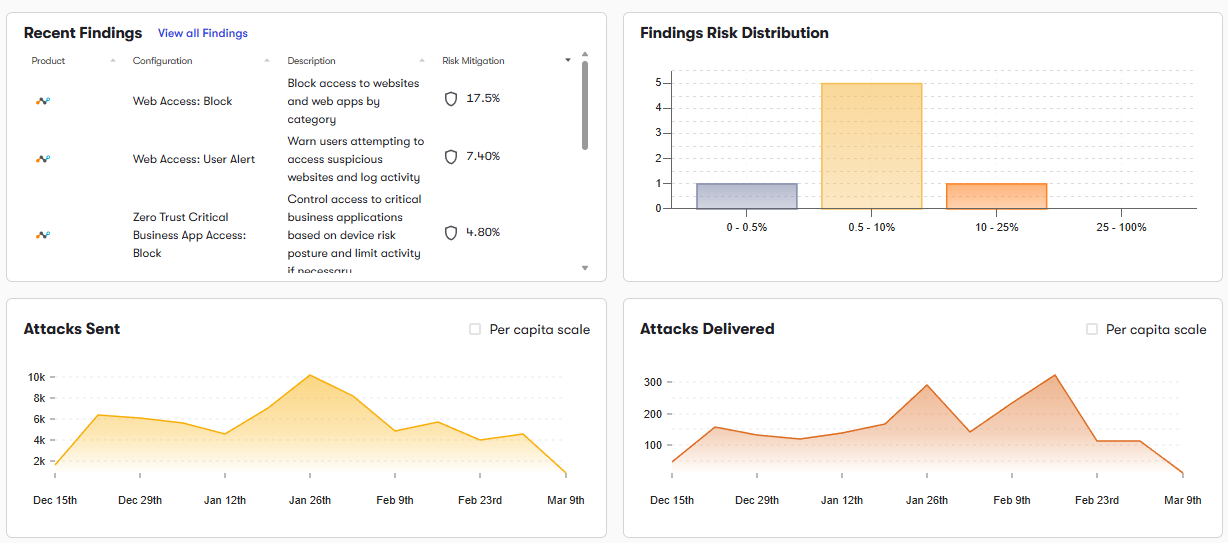
Get the reportBut over time, Netskope security controls can drift from their intended state. Changes to protection policies, SSL inspection, and SaaS governance can create gaps that allow risky traffic and unsanctioned apps to go unchecked.
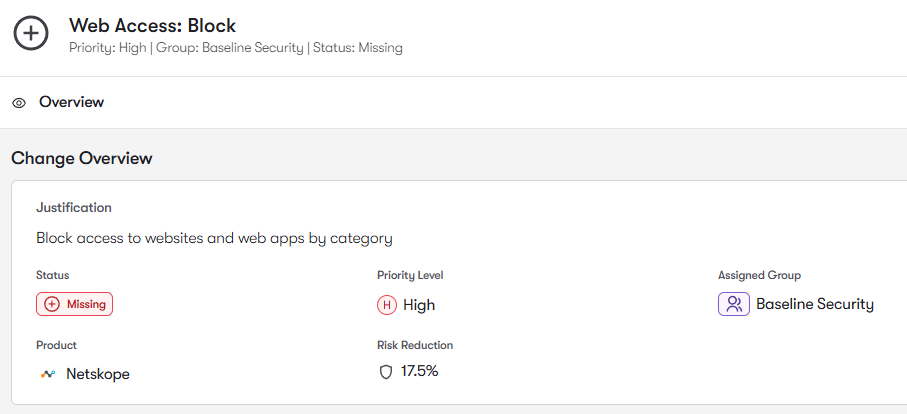
Netskope Secure Web Gateway policies rely heavily on Real-time Protection Policies that enforce URL filtering, threat protection, and acceptable use controls. Reach analyzes these policies to identify and remediate overly permissive URL category rules, unsafe category allowances, and policy exceptions that bypass inspection.
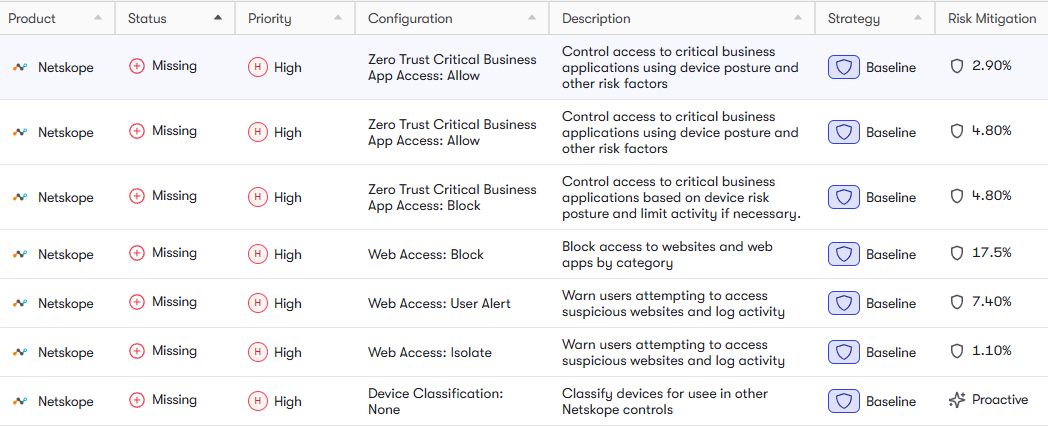
Modern threats frequently hide inside encrypted traffic. Netskope’s SSL inspection policies detect malware, command-and-control traffic, and malicious downloads within HTTPS sessions. Reach analyzes SSL inspection coverage, certificate deployment, and policy exceptions to identify traffic that bypasses inspection. It also surfaces gaps where Advanced Threat Protection or sandboxing features may not be fully enforced.
Netskope’s CASB capabilities allow organizations to govern thousands of SaaS applications and control how users interact with apps. Reach analyzes SaaS App policies and controls to identify risky SaaS access patterns, and surface situations where users can upload, share, or download sensitive content from unsanctioned applications. This reduces shadow IT exposure across applications.
Netskope provides Data Loss Prevention (DLP) policies to regulate outbound traffic and prevent sensitive data exfiltration. Reach analyzes DLP policy enforcement, data identifiers, and inspection coverage to identify policies that exist but are not actively enforced across web or SaaS channels. Reach helps prevent sensitive data exposure and reduces the risk of attackers establishing outbound command-and-control channels.
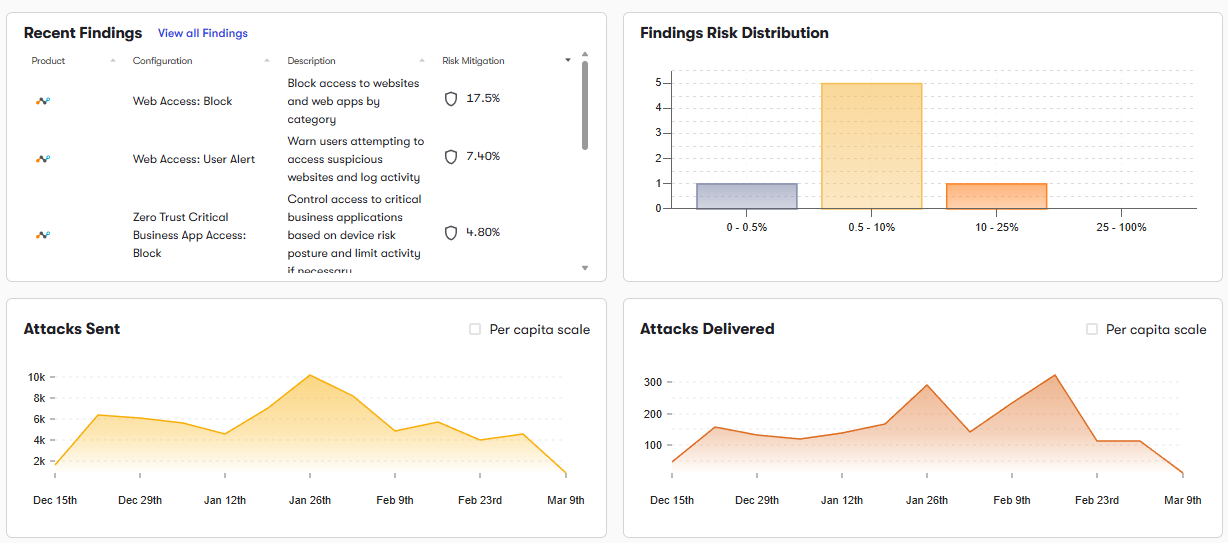
As administrators update policies and introduce new rules, Netskope configurations can gradually drift from intended security posture. Reach continuously monitors changes across your Netskope deployment. When drift is detected, Reach alerts security teams and recommends corrective actions. This continuous validation ensures Netskope protections remain consistent and effective.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: