Just Released: Reach Recognized in Gartner® Emerging Tech Report on Domain-Specific Language Models for SecOps
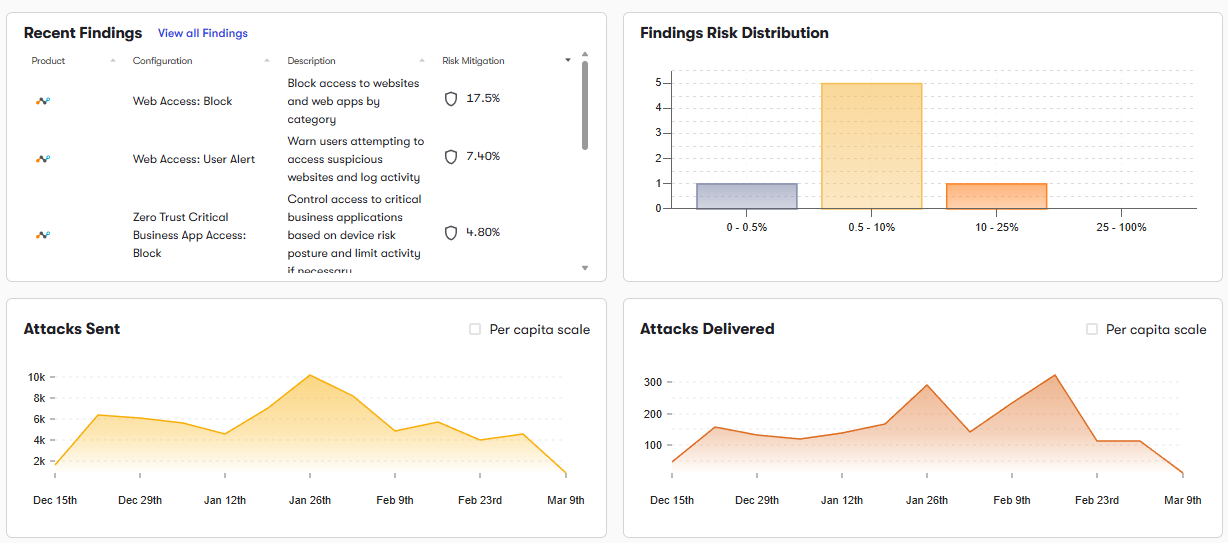
Get the reportOver time, Application Segments, Access Policies, and Posture Profiles can drift, creating overly broad access or segmentation gaps.
Reach analyzes Application Segments and Segment Groups to identify overly broad definitions or weak isolation. Tightening these ensures users only access required applications.
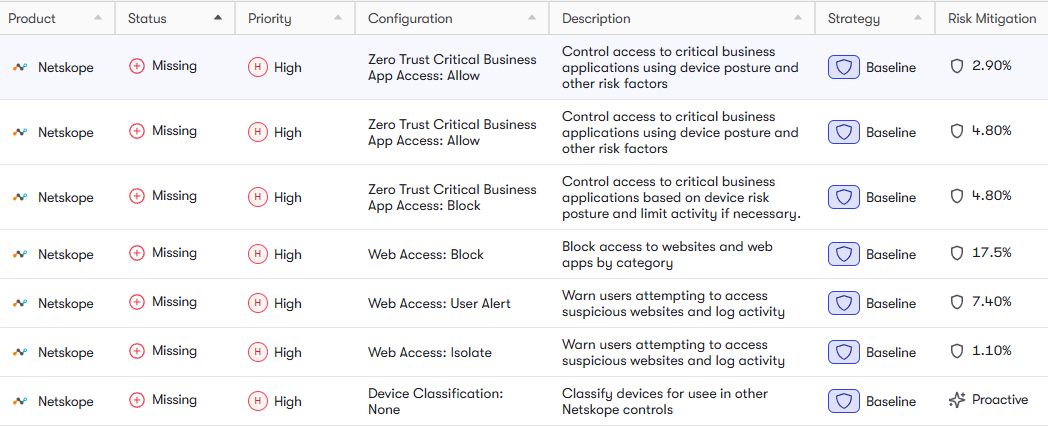
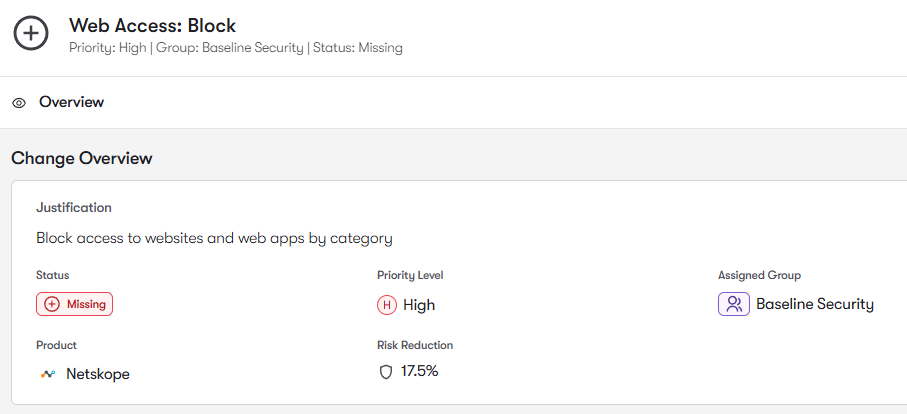
Reach analyzes Access Policies to identify permissive conditions, broad group assignments, and rule conflicts. Strengthening these ensures proper identity-based enforcement.
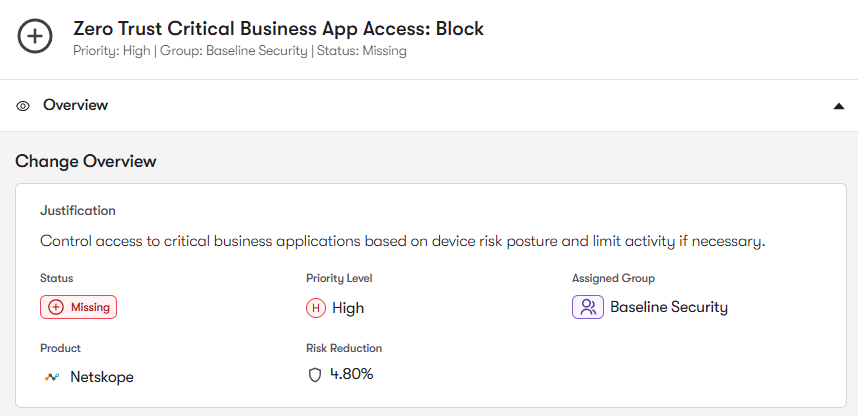
Reach evaluates Posture Profiles to identify weak or missing device checks. Strengthening posture enforcement ensures only trusted devices can access applications.
Reach analyzes App Connector deployment and segmentation to identify gaps or misconfigurations. This ensures applications remain securely segmented and properly accessed.
To join the community of customers enjoying the benefits of Reach and learn more about how it can transform your security posture, visit: